Control Center Users
HYPR Control Center Advanced: Global Settings Menu
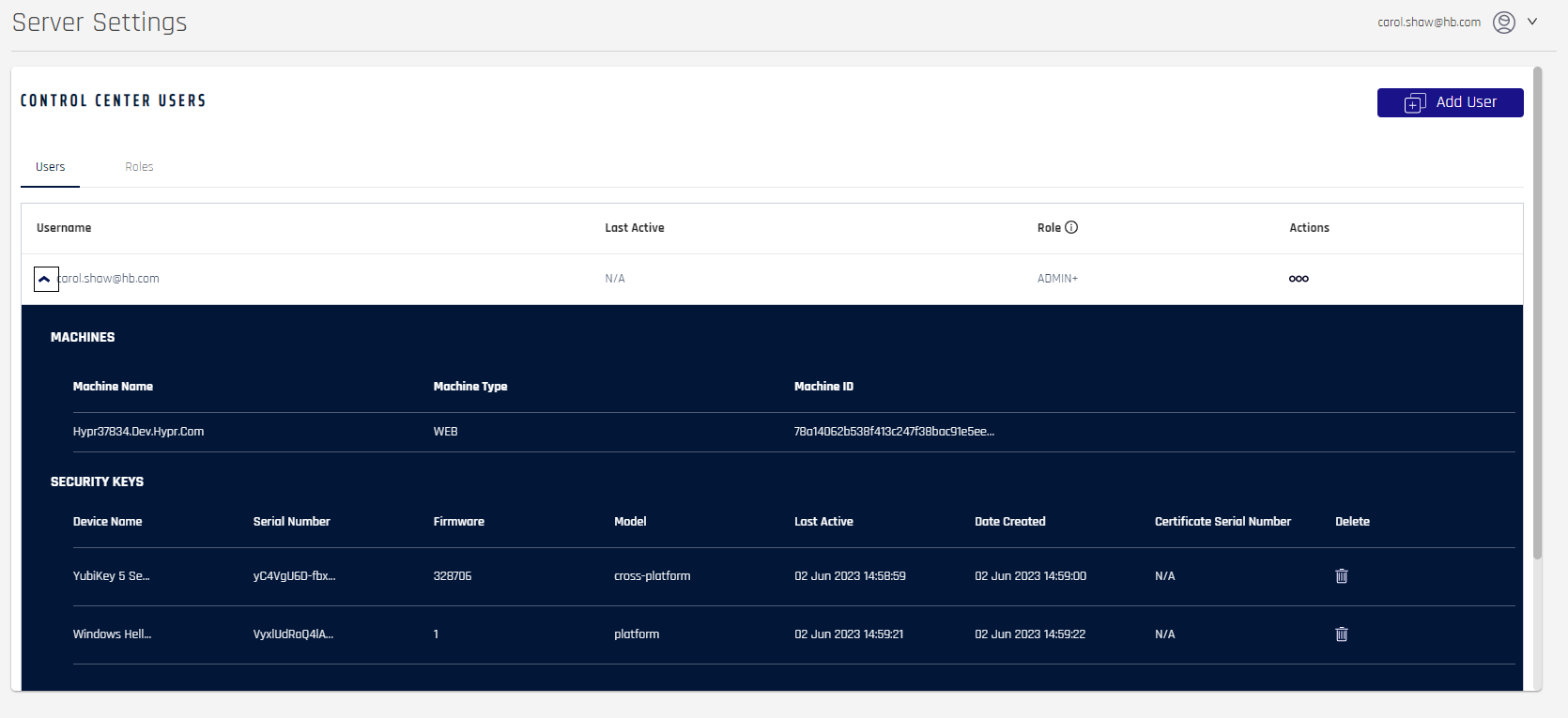
In addition to regular users (who unlock their workstations or log in to web applications with HYPR), the Control Center also has a separate set of admin users. Depending on their assigned role, these Control Center Users can perform back-end actions such as creating RP Applications, changing registration and authentication policies, monitoring user activity, creating Access Tokens, and generating Recovery PINs. Unlike regular users who are added when they register a mobile device, Control Center User accounts must be created manually.
Control Center User Roles
All Control Center Users are assigned a role when they’re added to the system. Depending on the role, the user may be limited to accessing only certain Control Center screens. The current role definitions are as follows:
| Role | Permissions |
|---|---|
| Admin | Has full Control Center administration rights, including: - Setting up and managing Applications within the Control Center - Changing global settings - Adding new Control Center Users - Reassigning user roles - Viewing the Audit Trail |
| App Manager | Can set up and manage Applications within the Control Center, including: - Managing policy and authenticator settings - Changing workstation access parameters - Customizing the Mobile App UI - Changing push settings - Generating Access Tokens - Creating Magic Links to invite new users - Viewing the Audit Trail (optional) |
| User Manager | Can manage users for Applications within the Control Center, including: - Creating Magic Links to invite new users - Deleting existing users - Viewing authentication history - Generating Recovery PINs for workstation unlock - Viewing the Audit Trail (optional) |
| Viewer | Cannot make changes but has limited access to all Applications within the Control Center, including: - Viewing the settings for Applications - Viewing the Audit Trail (optional) |
| Basic Logon | Can use HYPR to authenticate passwordlessly - No access to Control Center - Only appears in the Roles tab - Not assignable with Add User |
Adding a Control Center User
Control Center Users who are assigned the Admin role can use the Control Center Users screen under the Global Settings menu to add and modify additional users.
Adding a new Control Center User is a two-part process. First you create the user, then you send them an automatically-generated Magic Link which lets them register their first mobile device and log in.
NOTE
The system automatically assigns the user’s email address to be the account ID. To associate aliases to usernames, see Username Aliases.
- Click the Add User button in the top right corner to show the Add User to Control Center dialog.
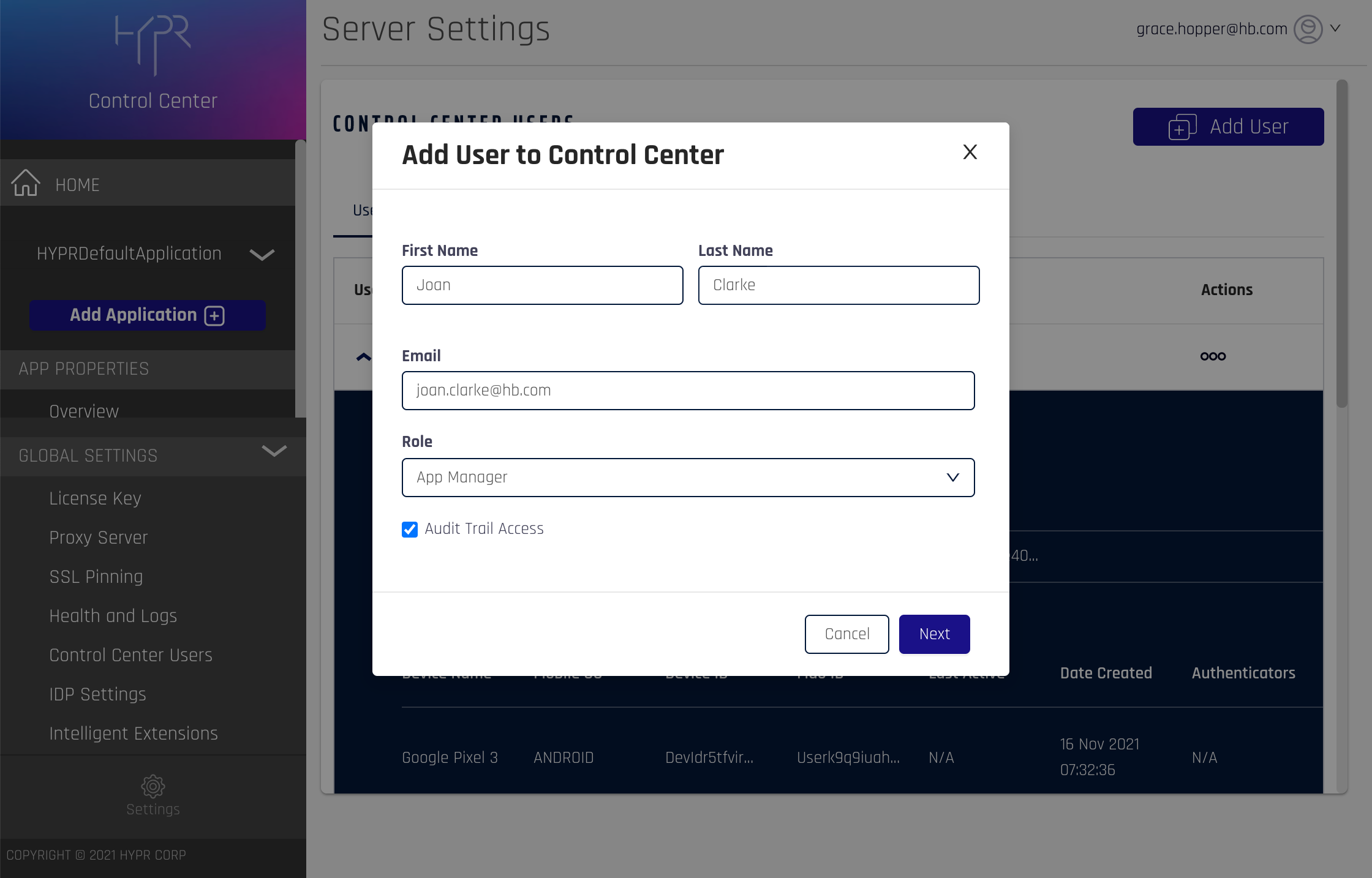
- Fill out the First Name, Last Name, Email, and Role fields. Check Audit Trail Access if you want to allow this user to view the Audit Trail page. Then click Next to continue.
+Audit Trail
Users who are granted optional Audit Trail access have a plus sign (+) next to their role on the main Control Center Users screen. Admins automatically have Audit Trail access that cannot be removed.
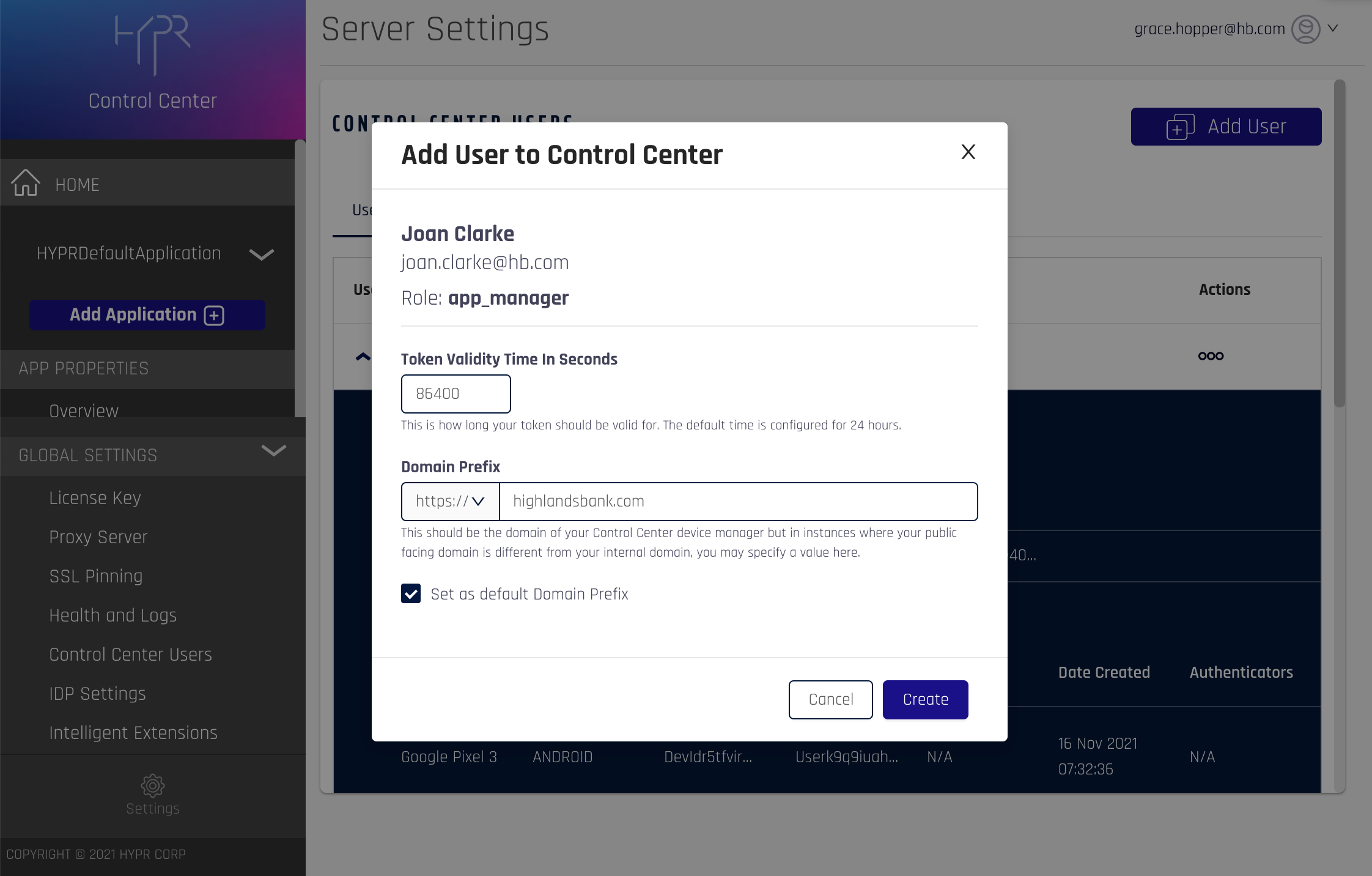
- Confirm the user name and email, then modify the default settings for the Magic Link if required:
| Setting | Definition |
|---|---|
| Token Validity Time In Seconds | By default, Magic Links expire 24 hours (86400 seconds) after creation. To change the validity period, enter your preferred duration in seconds. For example, use 600 if you want the link to expire after 10 minutes. |
| Domain Prefix | The specific domain for which you want to create the Magic Link. The Domain Prefix is configurable in case your public-facing domain is different from your internal domain. For example, if your Control Center instance is behind a firewall or DNS, you can enter the specific URL in this field. |
- Click the Create button to generate a Magic Link.
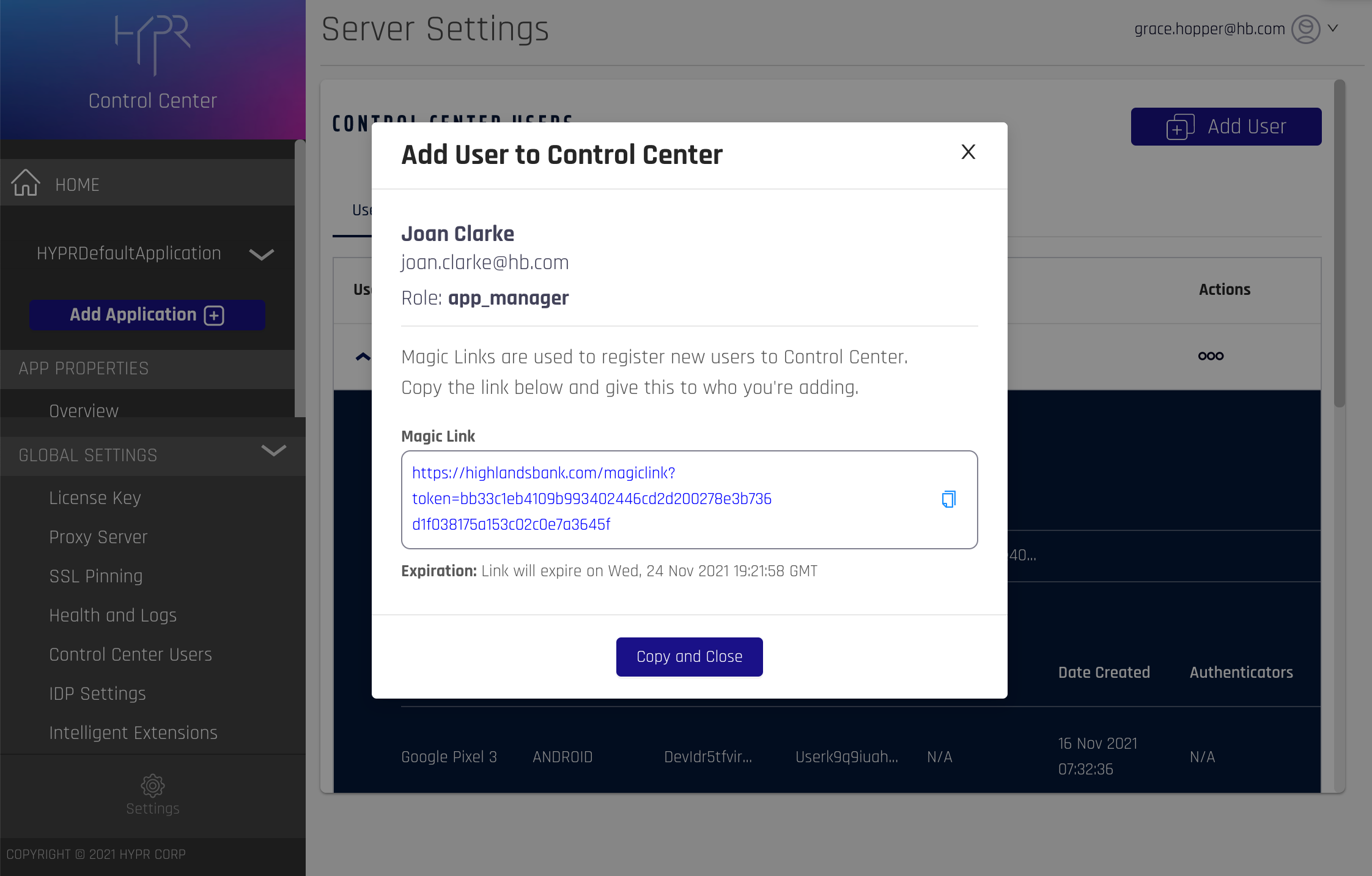
- Click Copy and Close to copy the Magic Link to the clipboard. You can then send it to the user via email or another communication channel.
Note that once you close the pop-up window, you won’t be able to view the Magic Link again. However, you can always generate another if necessary (see Modifying a Control Center User).
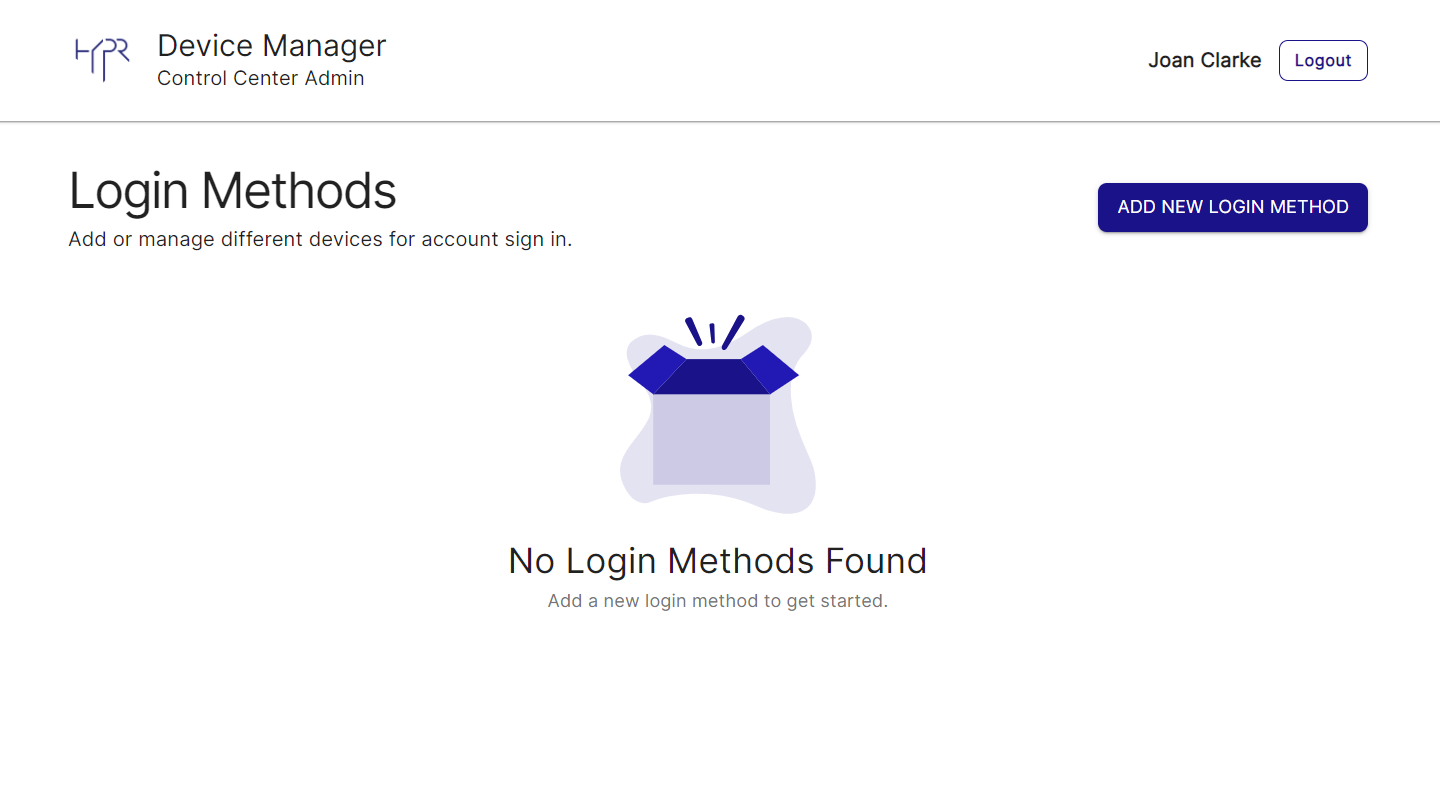
Using the Magic Link
Magic Links are designed to be opened in a browser and will take users to the HYPR Device Manager where they can begin the device registration process by scanning a QR Code.
Example:
https://highlandsbank.com/magiclink?token=bb33c1eb4109b993402446cd2d200278e3b736d1f038175a153c
02c0e7a3645f
Modifying a Control Center User
To modify an existing Control Center User, locate their account on the Users tab and click the icon in the Actions column.
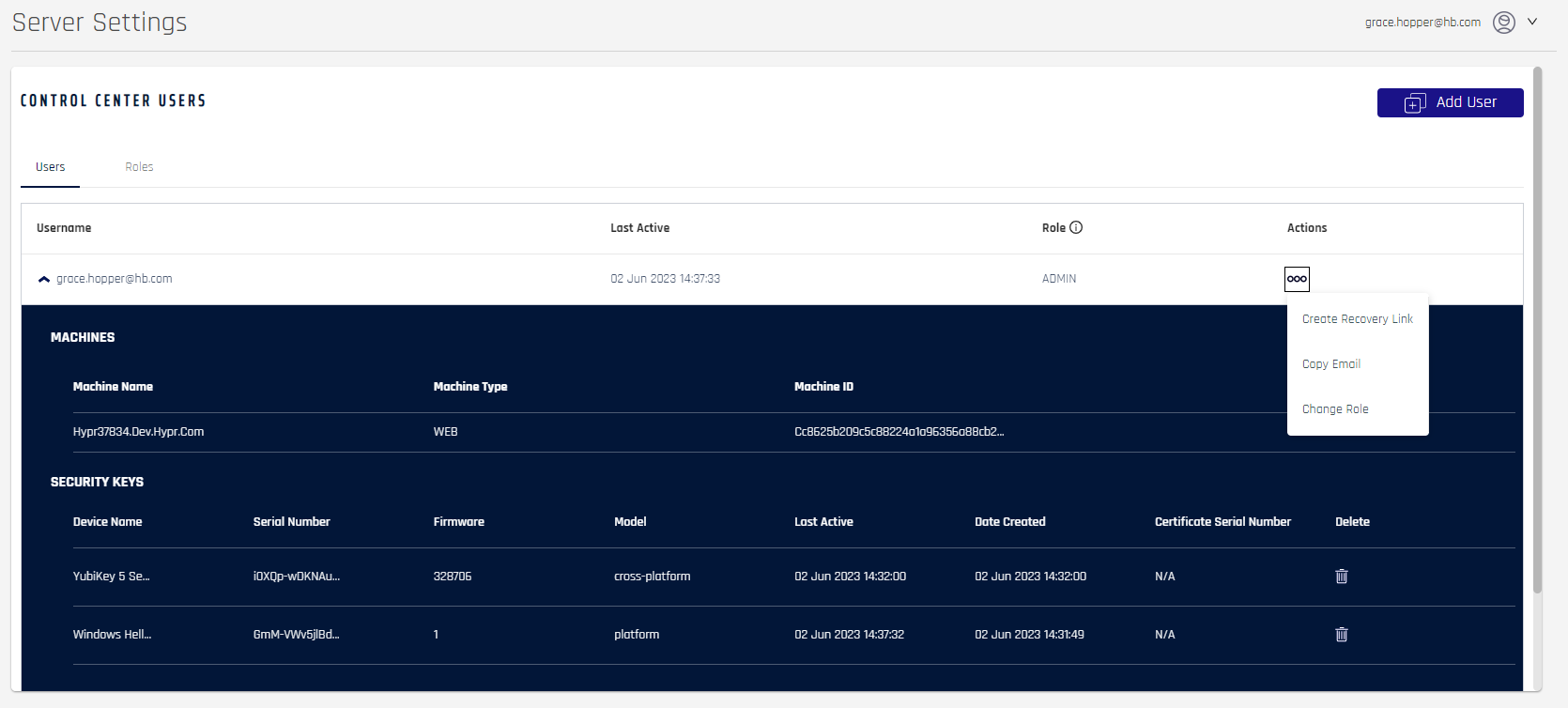
Four available actions appear in the dropdown menu:
Create Recovery Link
Regenerates a Magic Link for the selected user. The link parameters and format are the same as when you create a new user (see Adding a Control Center User).
Copy Email
Copies the selected user’s email address to the clipboard.
Change Role
Changes the selected user’s assigned role and/or optionally assigns access to the Audit Trail page.
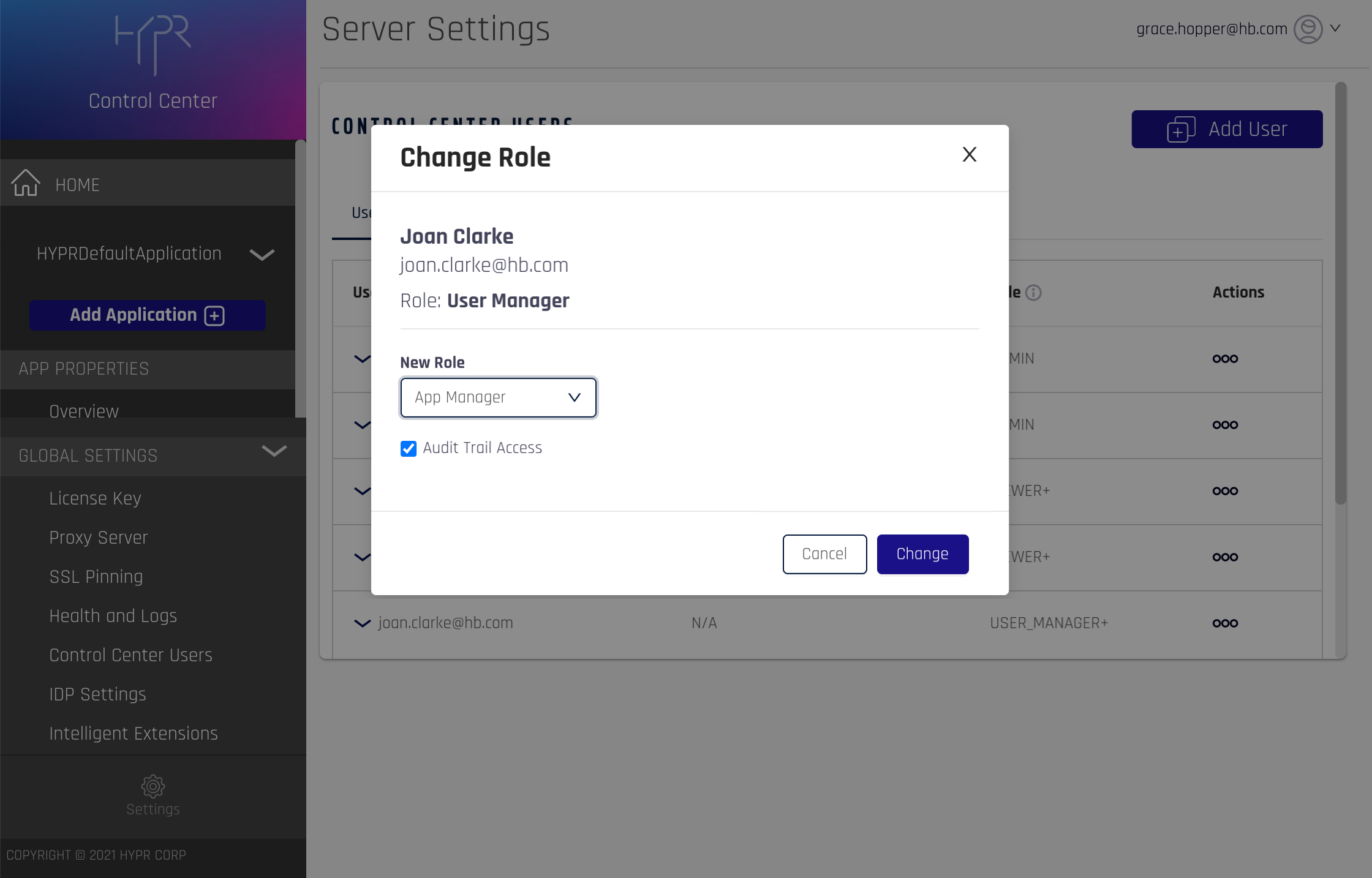
Affected Users
Users who are logged in when the role change occurs will need to log out and log back in for the change to take effect.
Remove
Deletes the selected user from the Control Center. This action can’t be undone, so you’ll need to confirm the deletion.
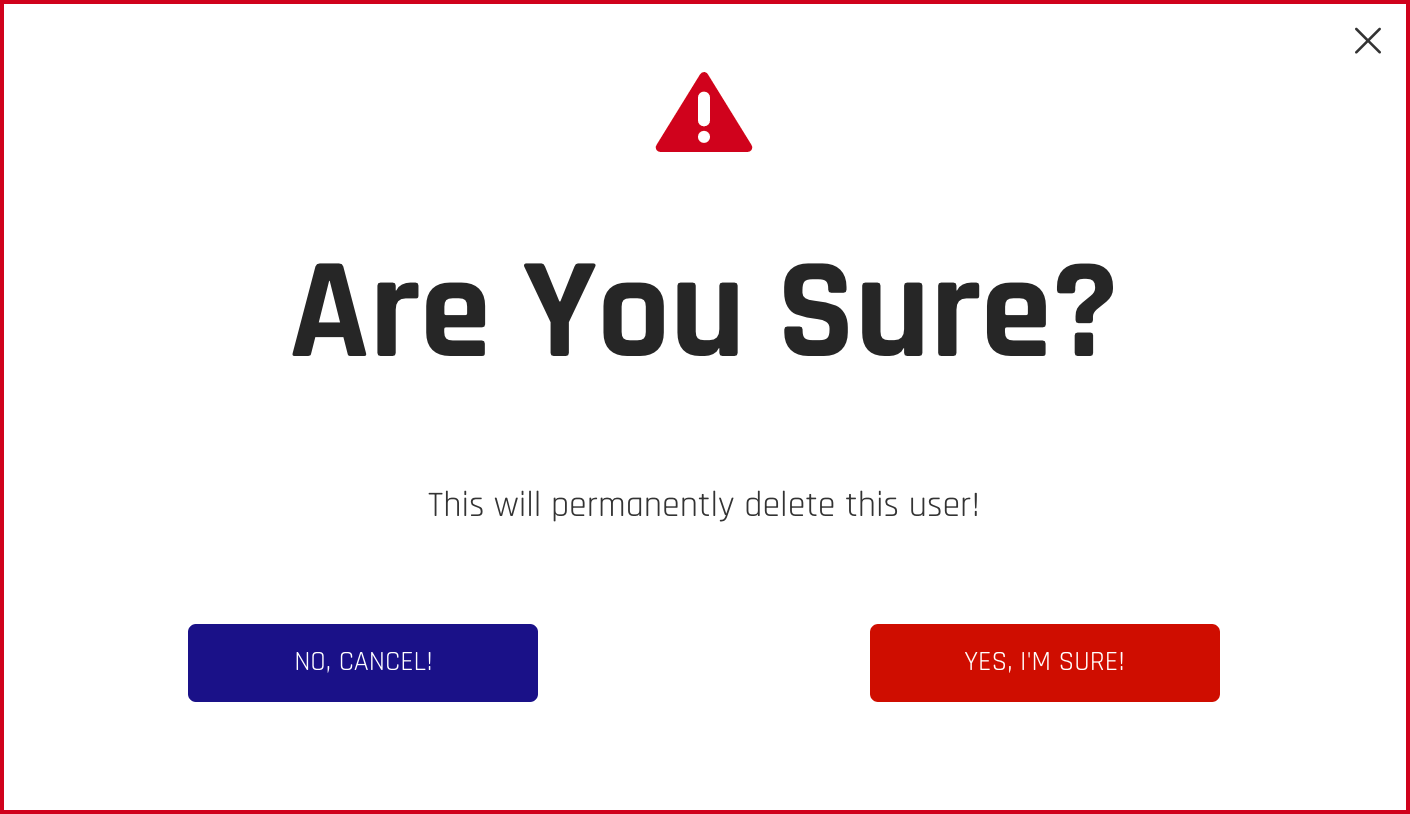
Safety First
To keep you from deleting your own account, the Remove option isn’t available for the current user.
Values shown in the list are identical to the ones in the CC Advanced App Properties menu, under User Management.
Viewing User Counts
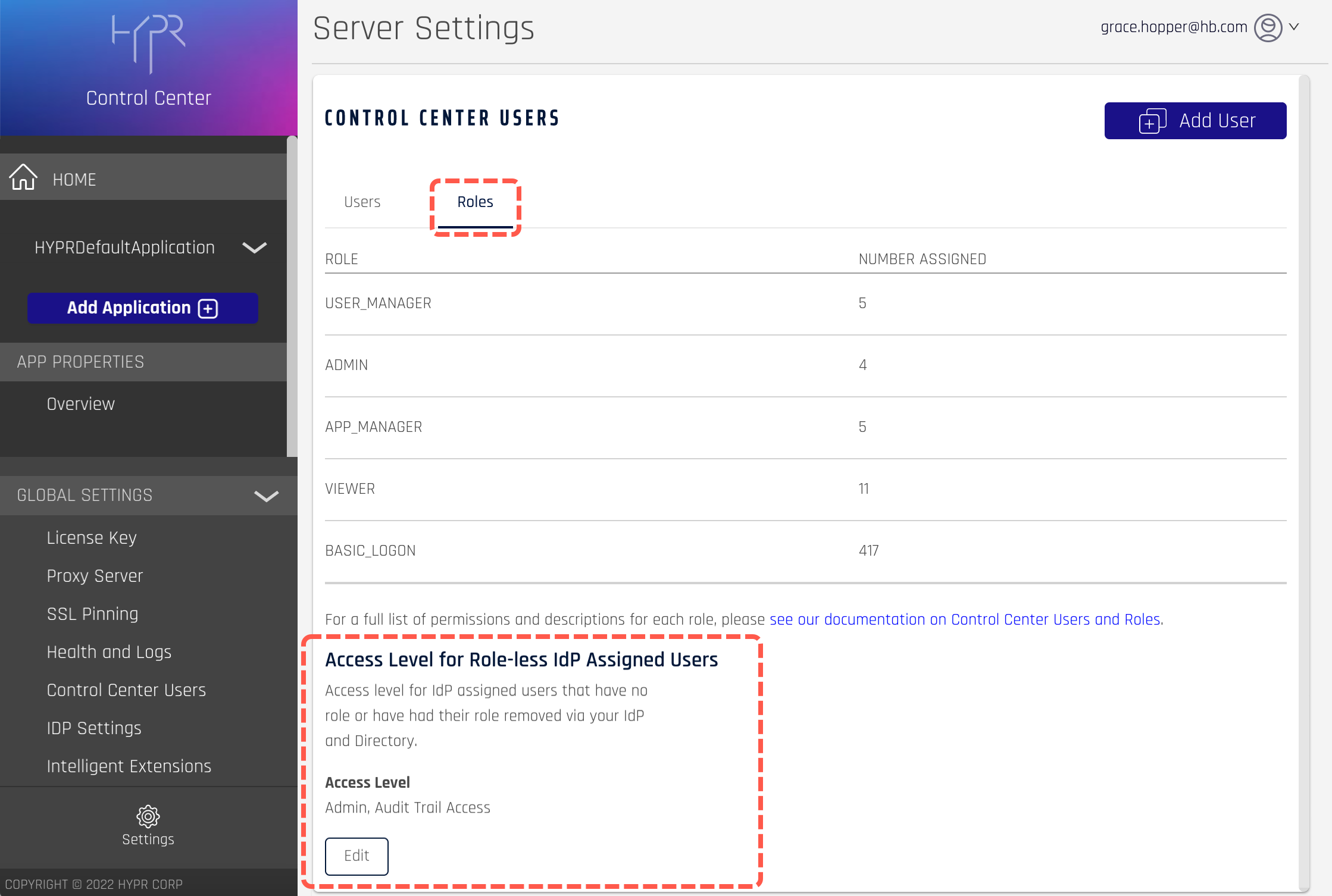
The Roles tab on the Control Center Users screen shows a summary of the users assigned to each account role. BASIC_LOGON indicates that the user can use HYPR to authenticate passwordlessly but has no access to the Control Center.
Mapping External IdP Users
For users who are logging in to the Control Center via an Identity Provider (IdP) such as Okta, you can assign and manage the Control Center roles externally as long as the IdP supports OIDC custom claims. You’ll just need to assign the roles within the IdP using the hypr_role custom claim.
| Custom Claim Name | Claim Value (User Role) | Claim Value (Audit Trail) |
|---|---|---|
| hypr_role | HYPR_ADMIN HYPR_APP_MANAGER HYPR_USER_MANAGER HYPR_VIEWER | HYPR_LOG_AUDITOR |
OAuth Version
If you’re using Okta as your IdP, the Control Center role mapping feature requires an OAUTH2 server that supports the most current API versions. Typically this means using the default authorization server that was created along with your account, whose base URL is
https://yourOktaDomain/oauth2/default.
Setting Default Roles
To set the default behavior for IdP-assigned users who don’t have a role defined:
- On the Roles tab Access Level for Role-less IdP Assigned Users section, click Edit.
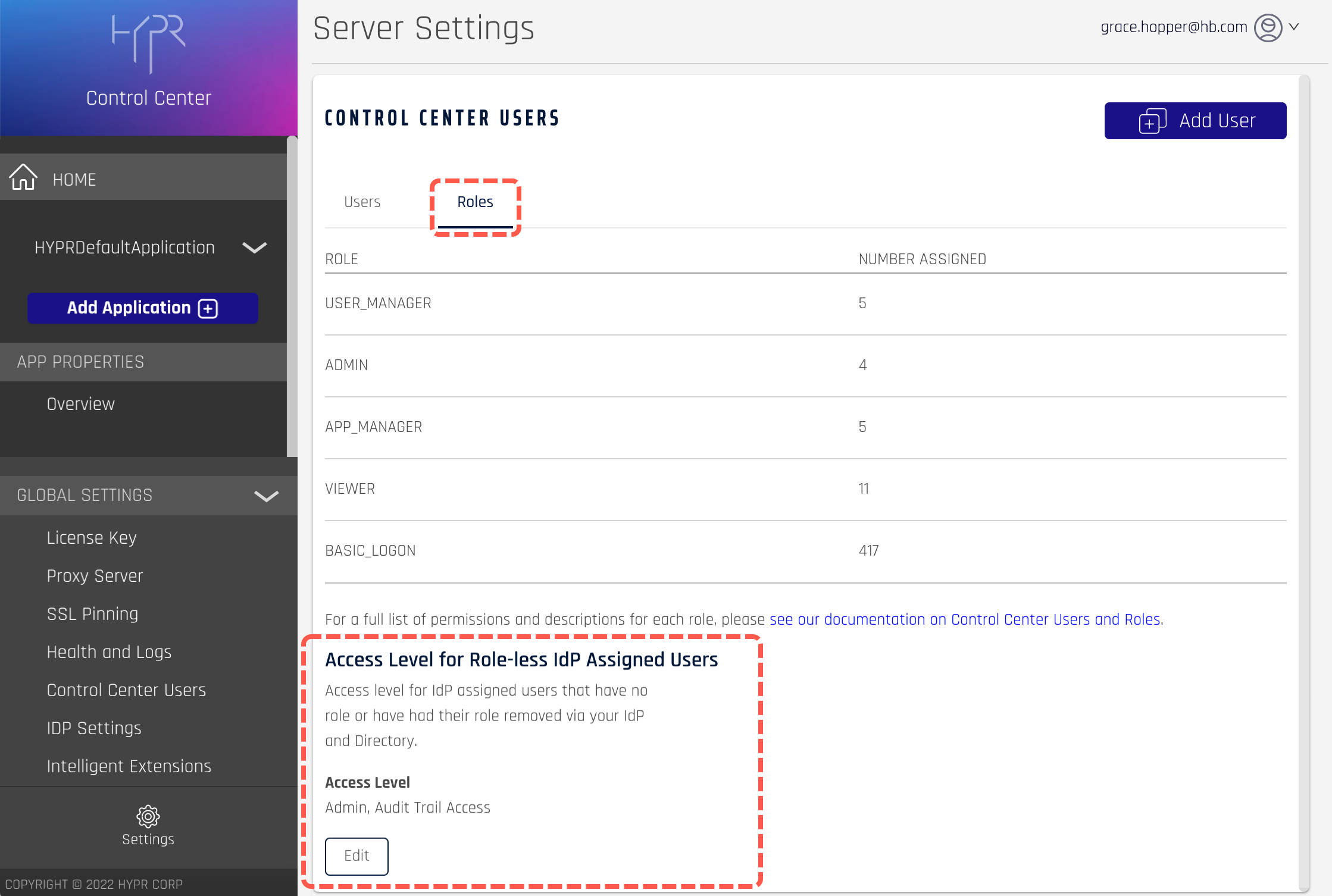
The section expands to show the available settings.
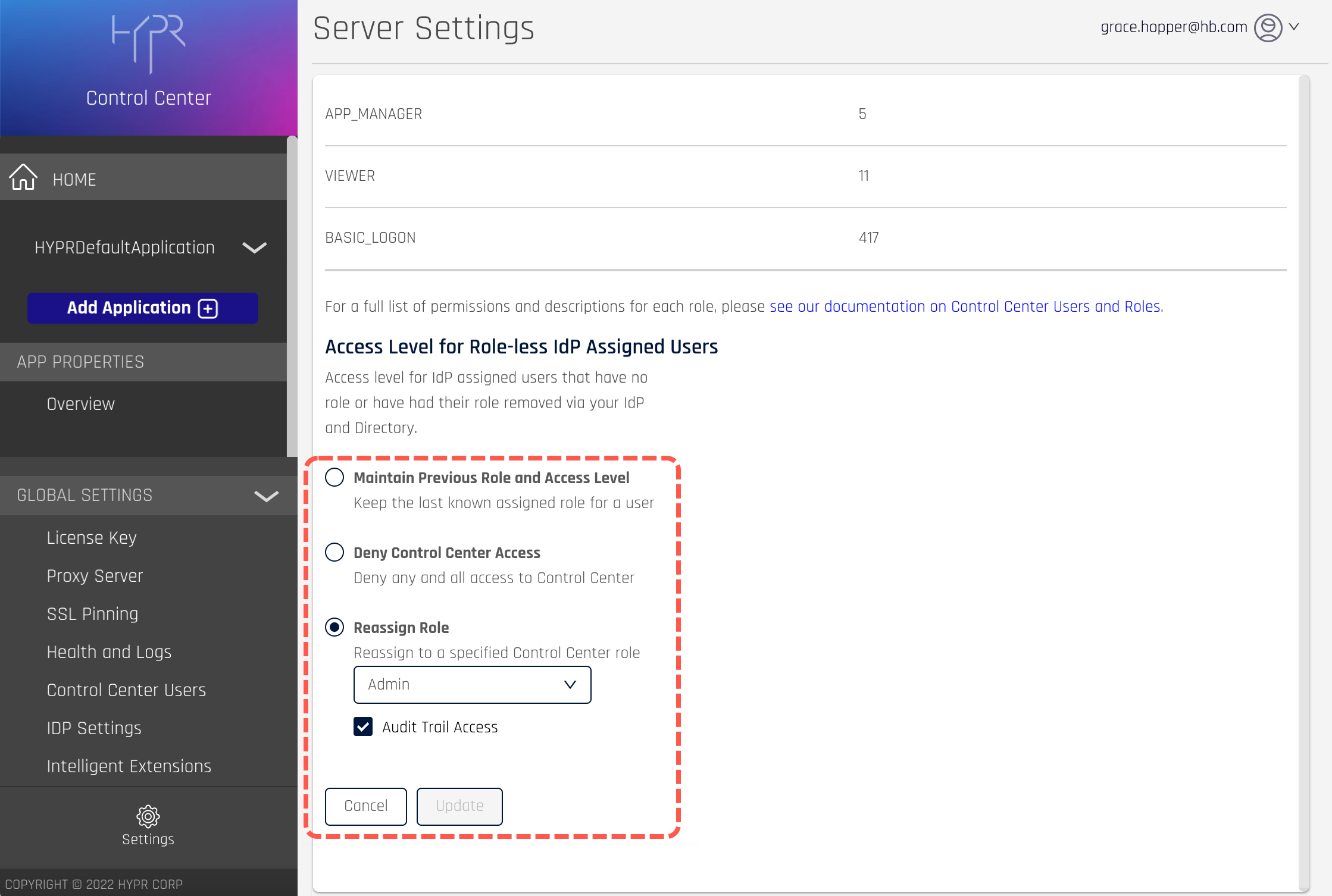
- Set the default access level as follows:
Maintain Previous Role and Access Level
Preserve the user’s last known role.
Deny Control Center Access
Block users from accessing the Control Center.
Reassign Role
Give users a specific role.
Audit Trail Access
Optionally assign access to the Audit Trail page.
- Click Update to save the changes, which will take effect next time the user logs in to the Control Center.
IdP Assigned Roles
Users whose role is defined externally will have “IdP Assigned” displayed next to their role on the main Control Center Users screen. You also cannot change their role from inside the Control Center.
Frequently Asked Questions
Q: What happens to Control Center Users created in older versions of HYPR, before roles were introduced?
A: Existing users will be assigned the Admin role by default but may be changed if required.
Q: What if an existing user has a non-email account ID?
A: Although newly added users will be given an email-format ID, existing non-email accounts will continue to work as before.
Q: Is recovery mode still available for Control Center Users?
A: Existing users may continue to use recovery mode if necessary. However, recovery mode won’t be available for new users.
Q: Why do some users have a plus sign (+) next to their role?
A: The plus sign means the user has optional Audit Trail access.
Q: Why doesn’t a role change seem to have any effect?
A: Role changes only take effect after the user logs out and back in again.
Q: Will users created in Okta automatically be added to the Control Center?
A: Yes. See Mapping External IdP Users for instructions on how to set a new user’s role.
Updated 5 months ago
