Okta: Identity Engine Integration in CC
This article is subject to change as the feature develops and we make improvements.
Integrating HYPR with Okta Identity Engine (OIE) lets you access your organization's Okta SSO-protected applications using HYPR passwordless authentication instead of the standard username + password login.
Getting the HYPR OIE integration up and running requires the following basic steps:
-
Understand how the Okta login process changes for end users after you integrate with HYPR. See What Will Happen in Okta?.
-
Configure the Okta side of the integration. See Setting Up Okta.
-
Configure the HYPR side of the integration. See Connecting Okta to HYPR.
The following HYPR Integration common tasks are explained on the Integrations main page.
-
Choose the methods you want people to be able to use for passwordless authentication; see Allowing the Use of FIDO2 Authenticators
-
Monitor integration-specific user activity with the Audit Trail
What You'll Need
-
HYPR Control Center Account: Since you're setting up the HYPR Okta integration through the HYPR Control Center, you should have already registered for an account, paired your mobile device with HYPR, and used your new passwordless login to access the Control Center. If this isn't the case, please contact us at https://support.hypr.com and we'll help you out.
-
Okta Admin Console Account: Although most of the HYPR Okta integration process is automated, you'll need an Okta admin account so you can change some configuration settings related to authentication policies.
What Will Happen in Okta?
Okta Admin Console
Because HYPR handles the setup for this application, you won't need to make any manual configuration changes. Each user enrolled via the HYPR Control Center will be automatically assigned to the application, and there are no routine maintenance tasks necessary on the Okta side.
When you add the HYPR Okta integration, HYPR will automatically create artifacts in Keycloak and in Okta.
-
A Device Manager application in the Okta Admin Console named after the
<rpAppId>you provided during setup (<rpAppId>)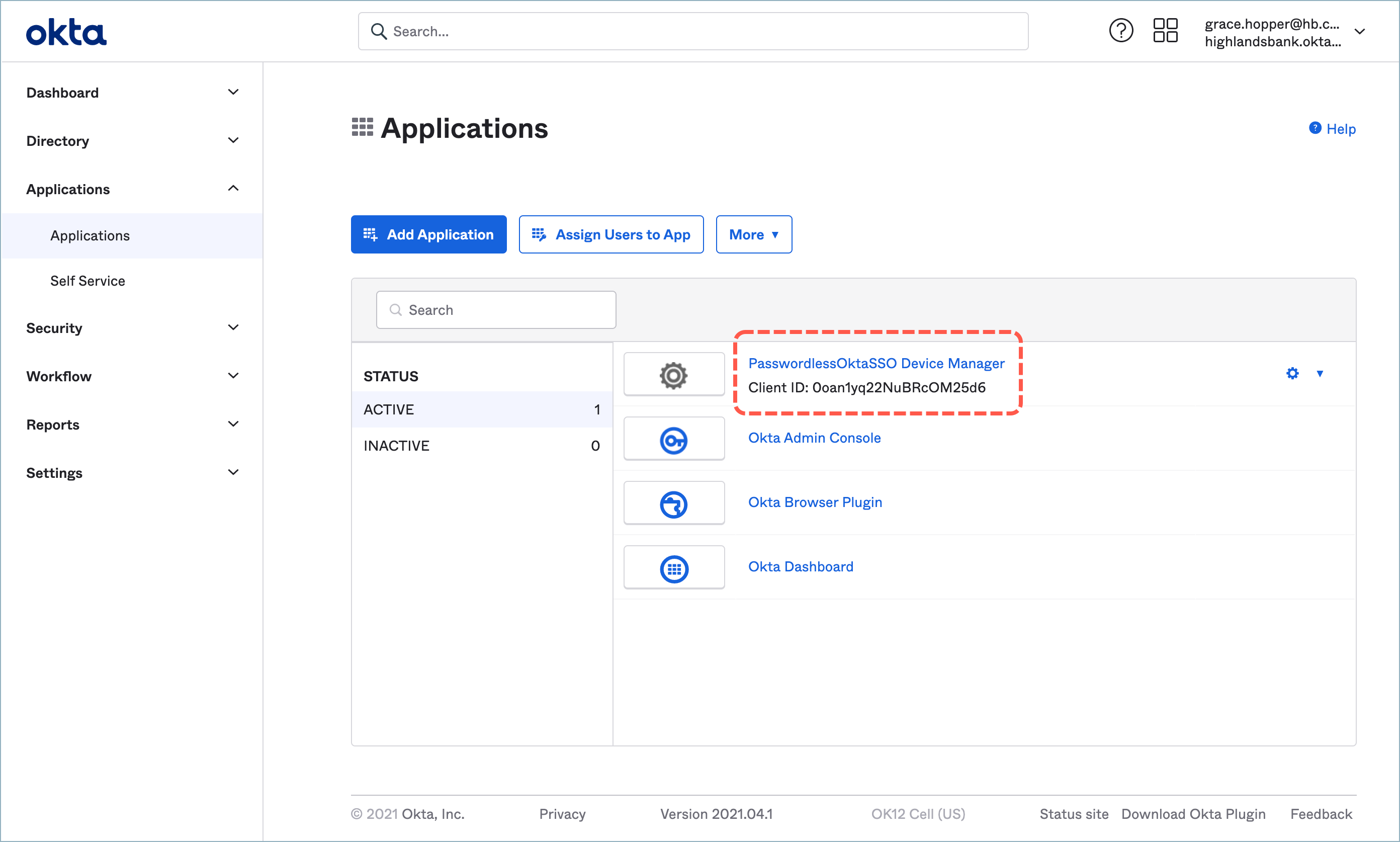
-
HYPR will create an Identity Provider based on the name you provide during setup
- This Identity Provider will contain an OIDC profile
-
A HYPR authenticator variable is generated with the name
hasHyprEAMDeviceRegisteredFor<rpAppId> -
An authenticator with
<rpAppId>as a name -
A group to include registered users if needed
User Experience
Okta User Home Page
Enrolled users will see the new Device Manager application listed on their Okta home page.
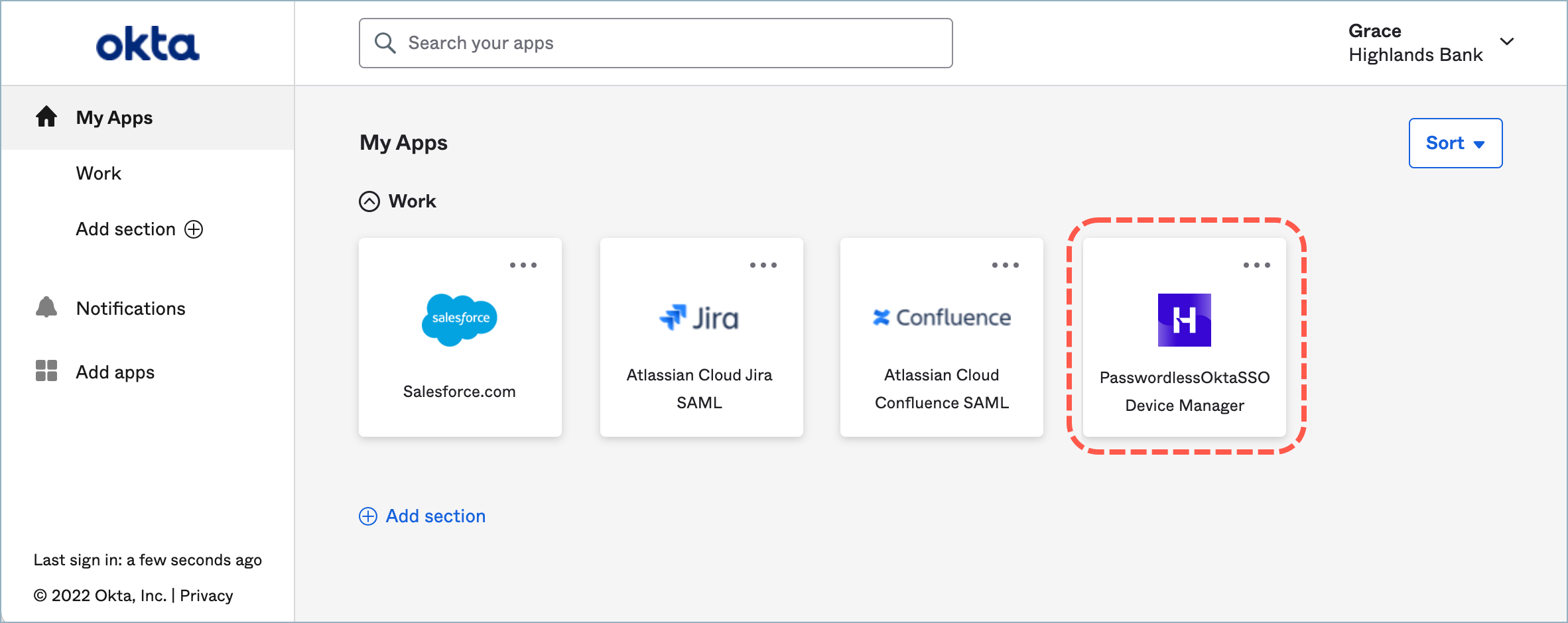
Clicking the application opens the HYPR Device Manager, where the user can add or remove the devices used for authentication.
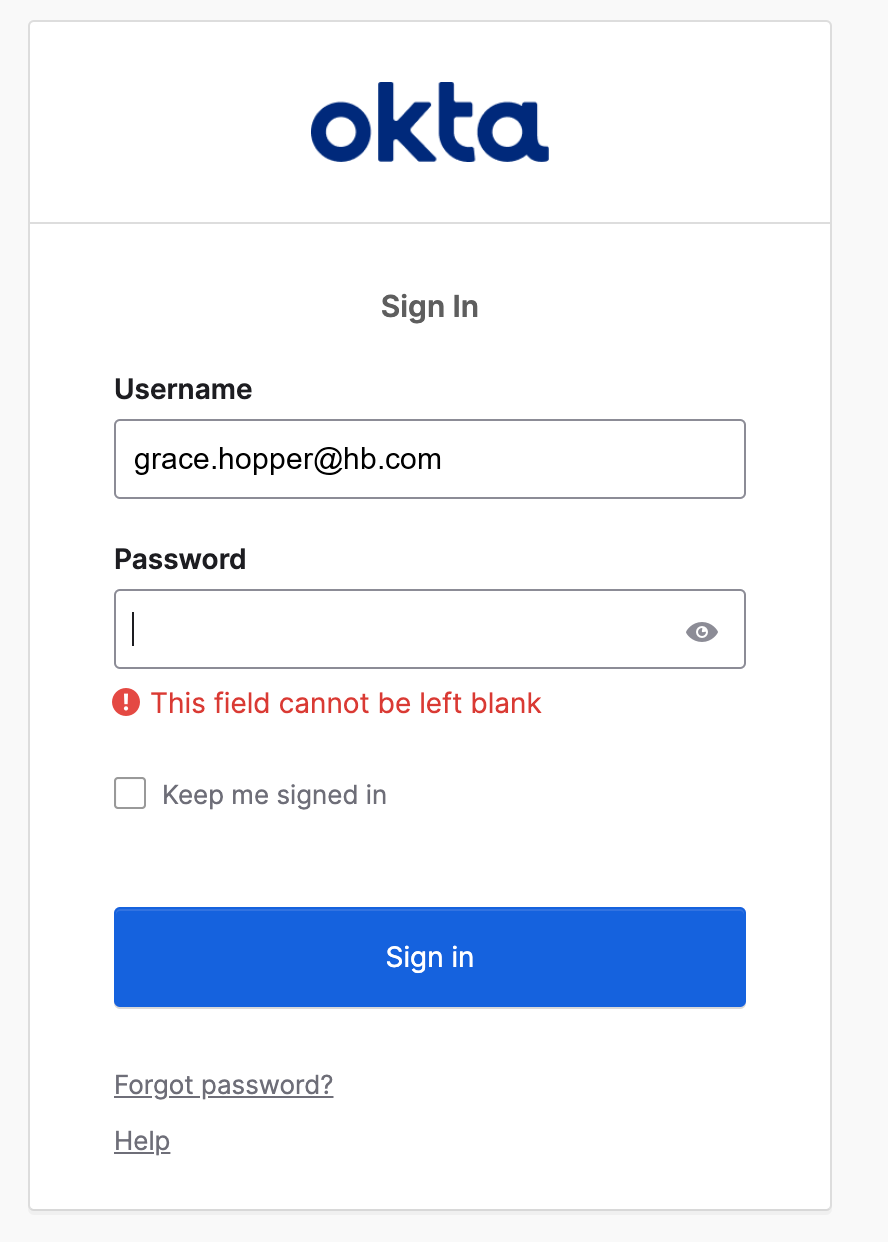
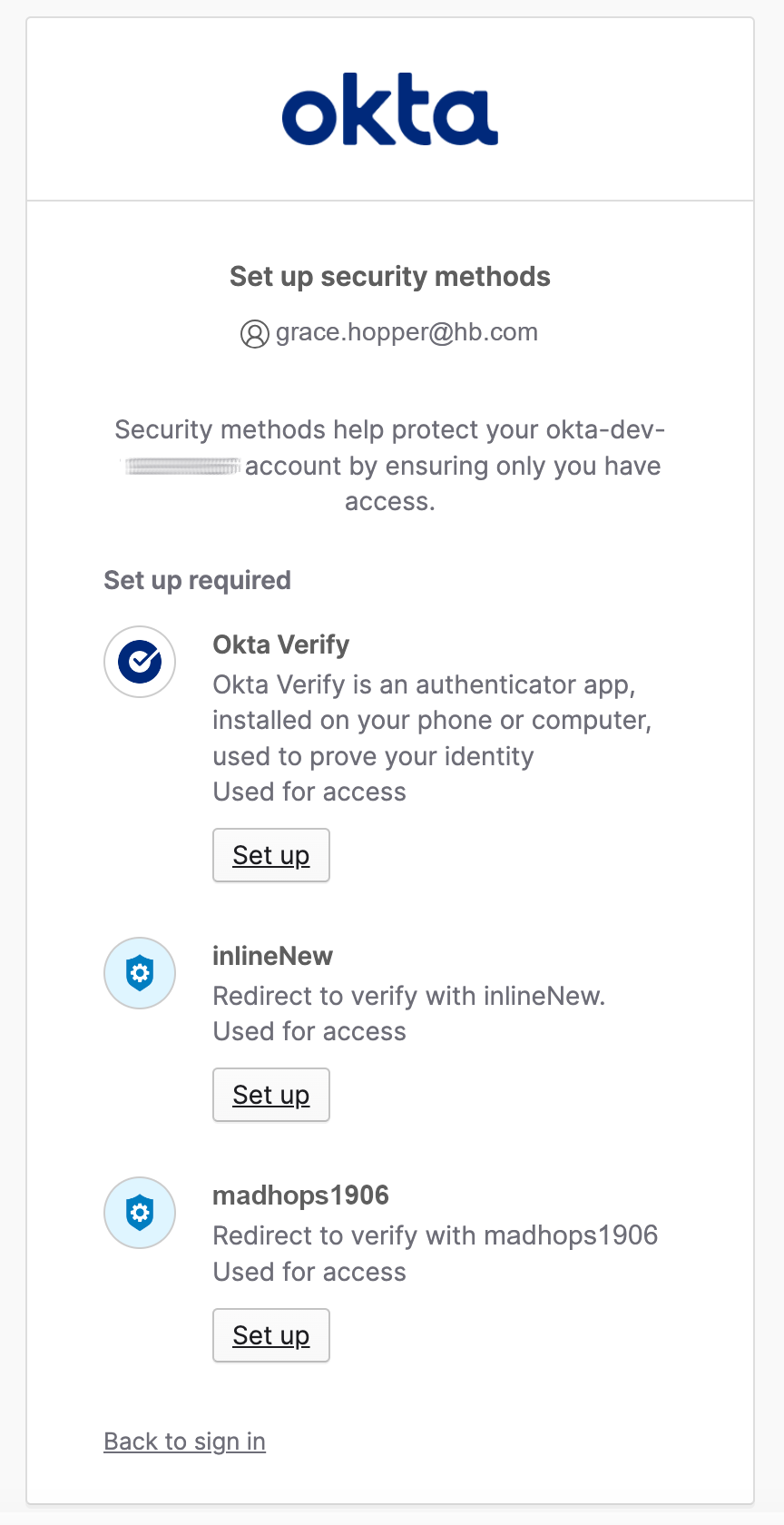
First-time Authentication
Okta will ask you to enter username and password, and to add a second authentication factor.
-
Enter username and password; click Sign in.
-
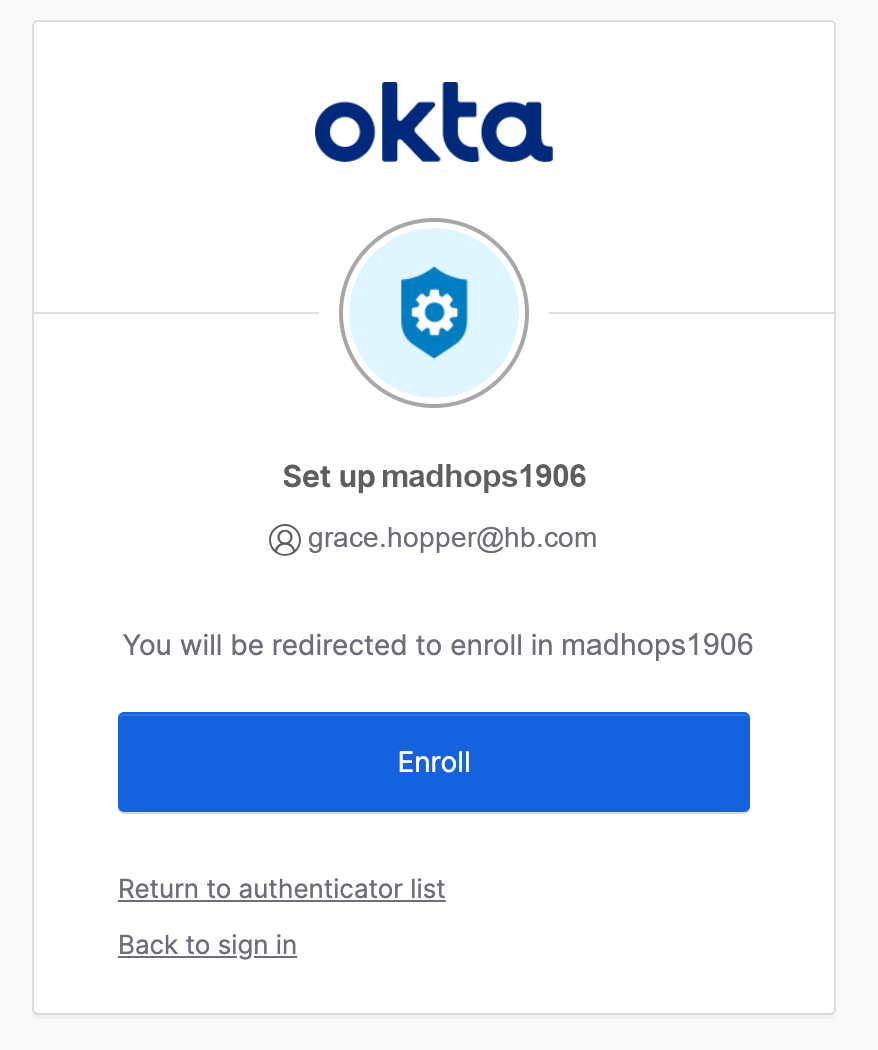
Setup your security method (in this case it is madhops1906) click Set up.
-
You are presented with an Enroll dialog. Click Enroll.
-
You will be forwarded to the Keycloak HYPR Login. Proceed to login using any available method.
-
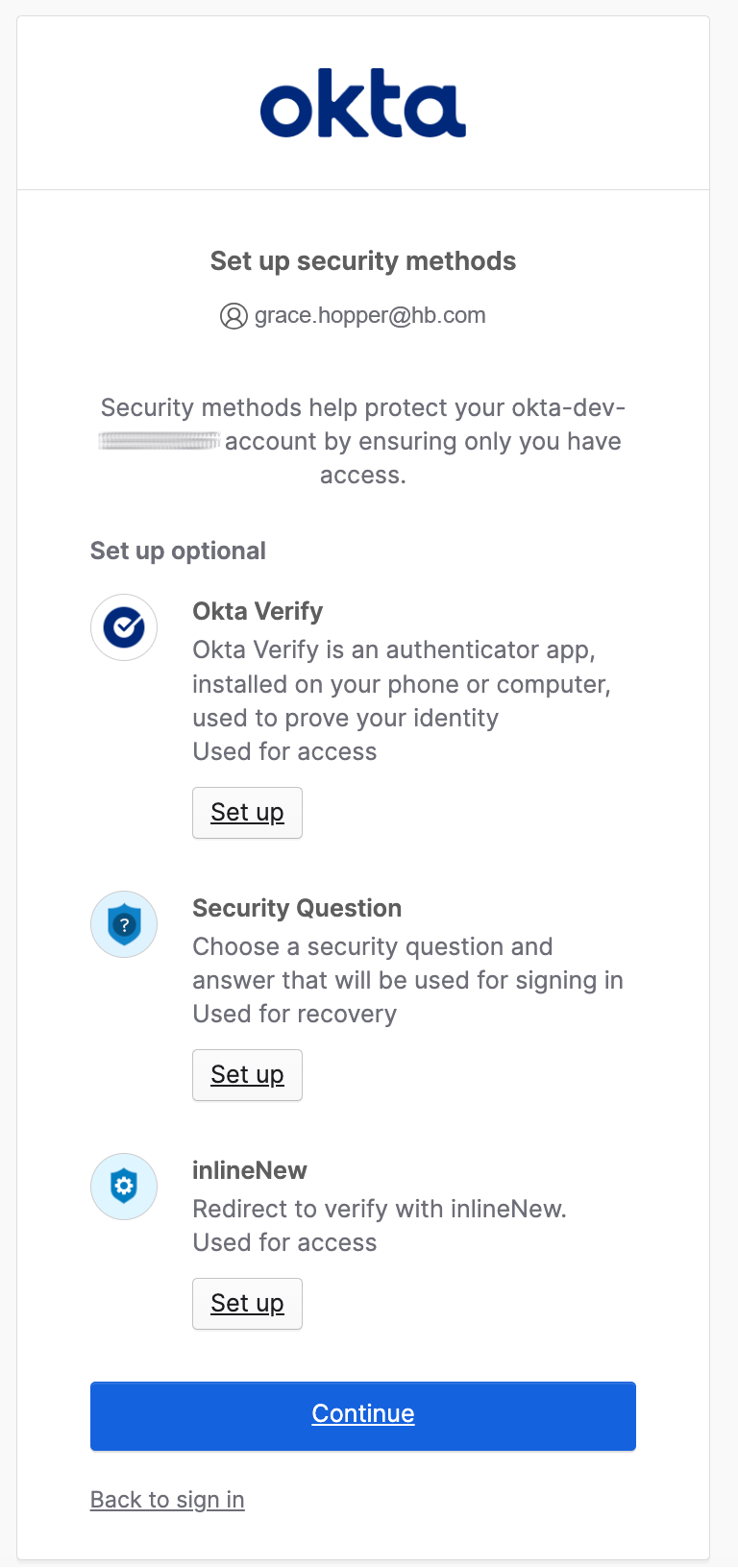
When you have finished loggin in, Okta will offer another chance to configure a new authentication method. Click Continue when you are finished.
Regular Authentication
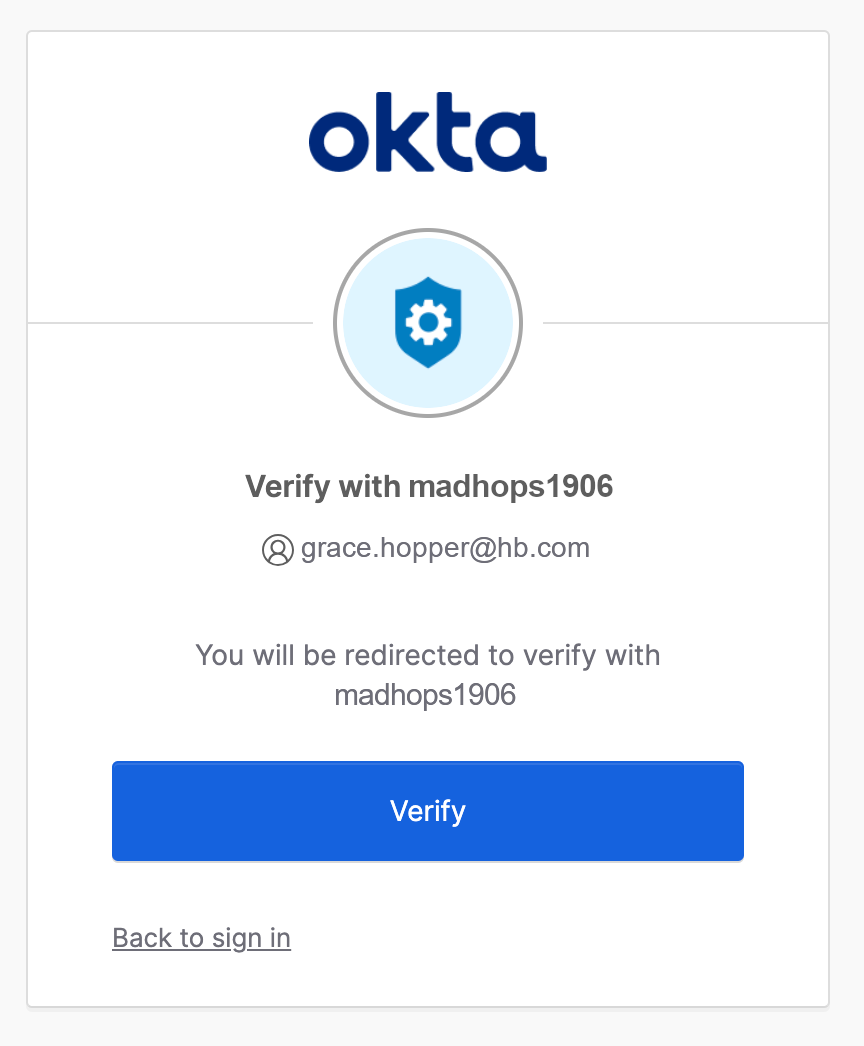
The next time you authenticate (and every time after that) you must enter your username and password, then verify your security method. Click Verify to be forwarded to HYPR to authenticate; once you have successfully authenticated via HYPR, you will be logged in to Okta.
Setting Up Okta
Okta Policy Pre-setting
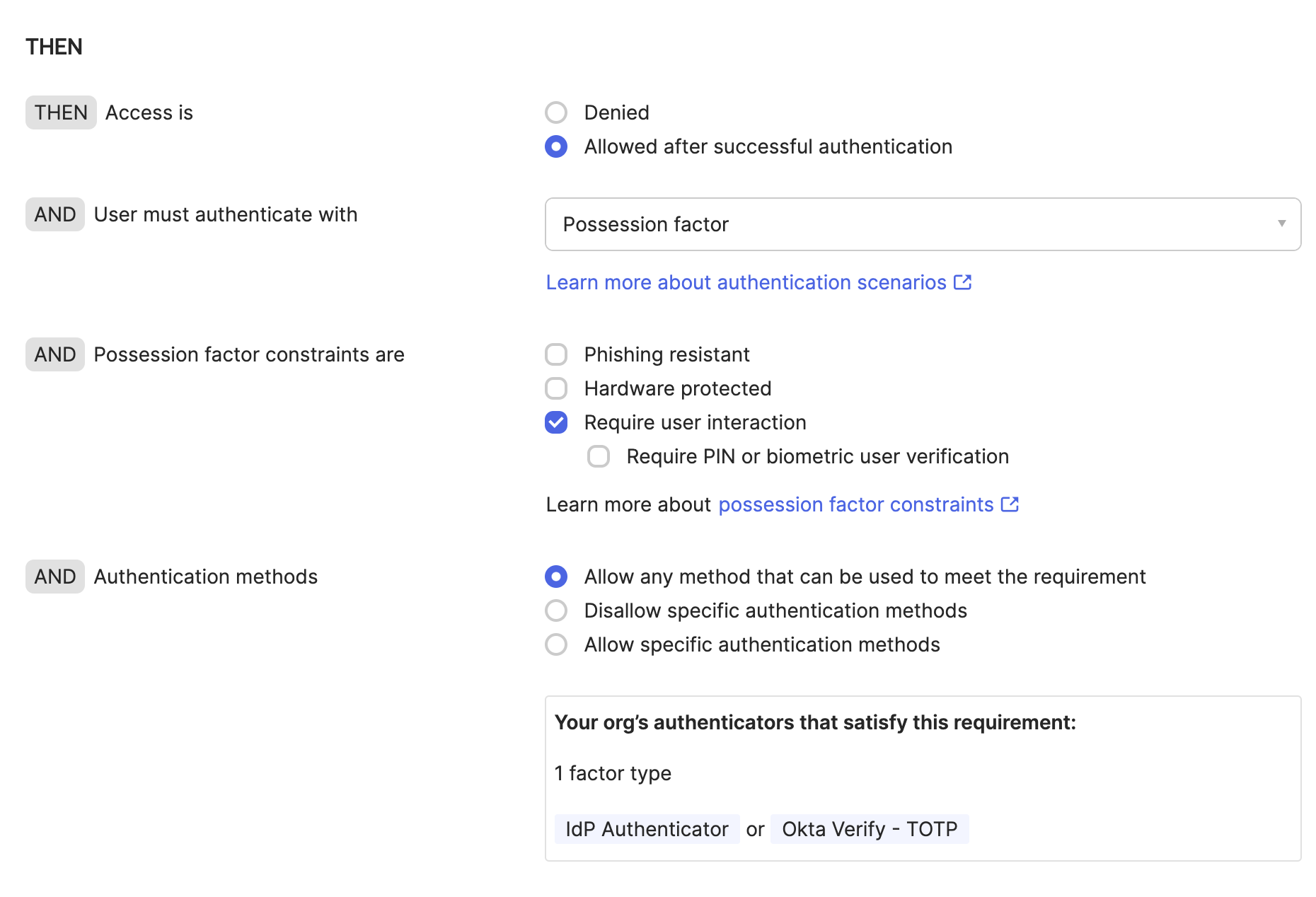
To enable the second factor for the tenant, set the Authenticator Policy.
-
In the Admin Console, go to Authentication Policies > Classic Migrated > Catch-all Rule > Action and Edit.
-
In THEN - AND User must authenticate with, use the drop-down to select Possession factor.
Connecting Okta to HYPR
-
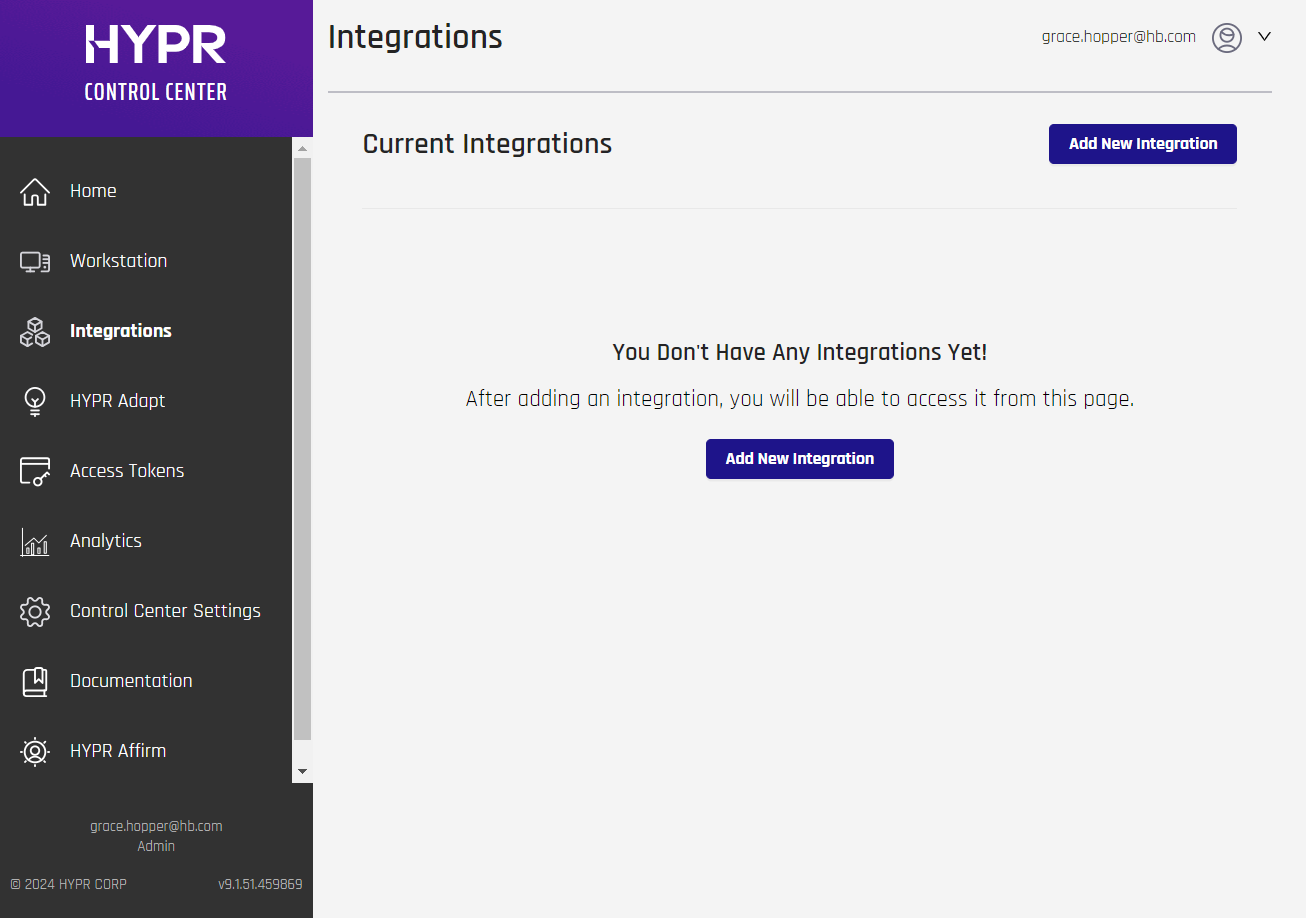
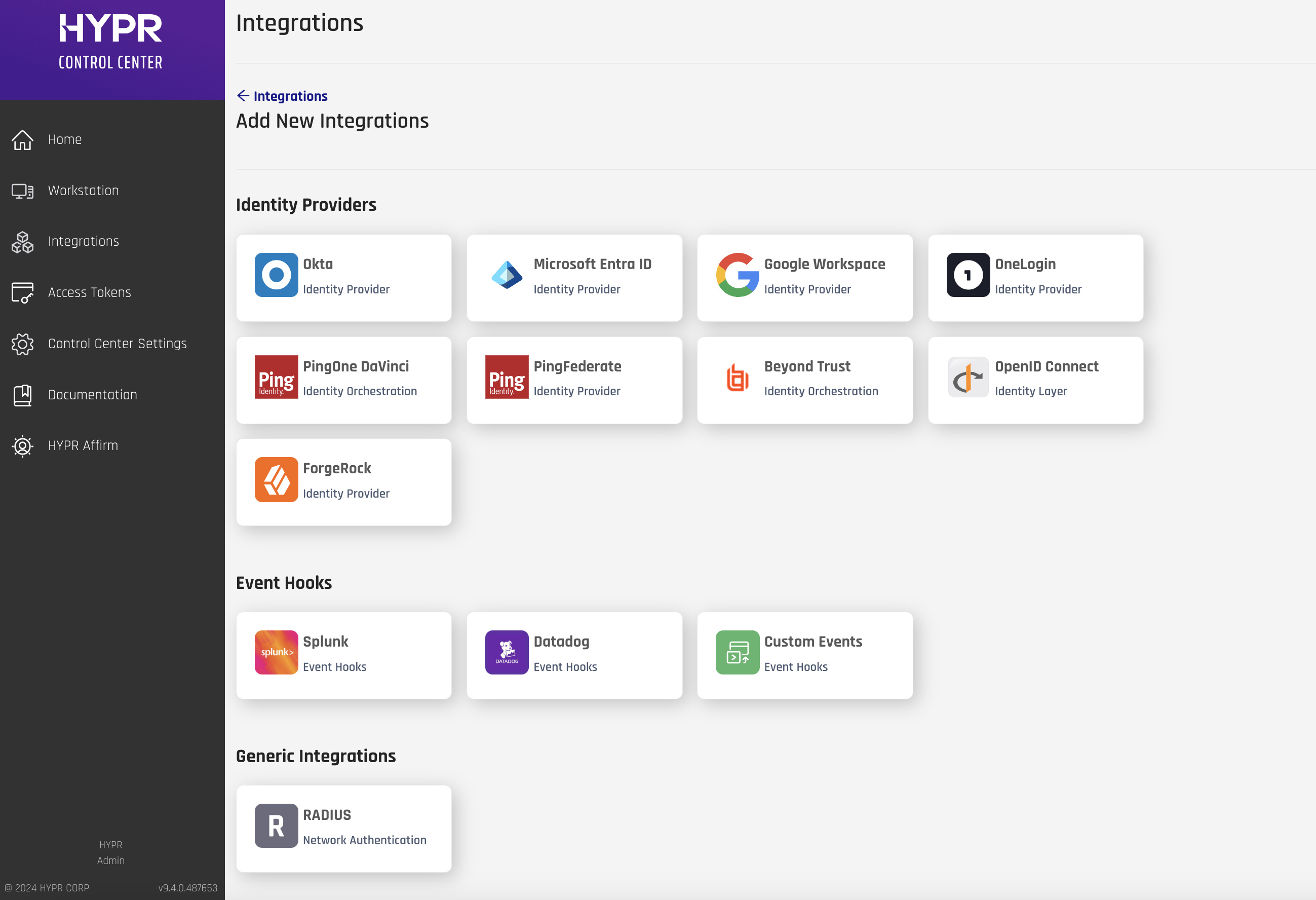
Go to the Integrations screen in the HYPR Control Center and click Add New Integration to show a list of available integration types.
-
Select the Okta Identity Provider integration.
-
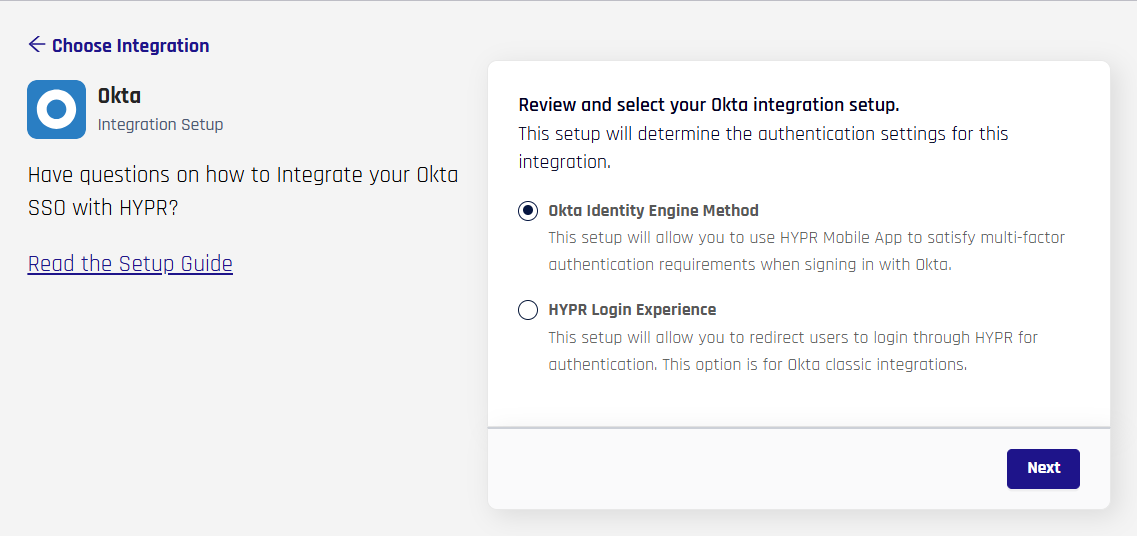
Select Okta Identity Engine Method, then click Next.
-
Provide some basic information on the Integrations screen as shown below.
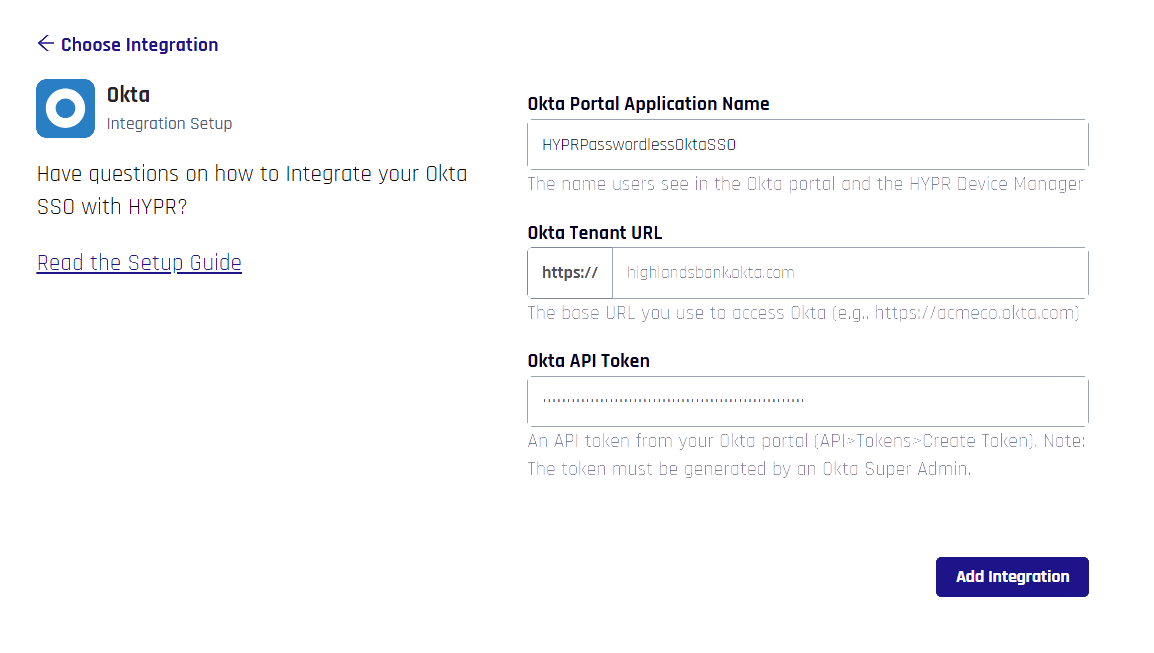
Field Value Okta Portal Application Name The name you provide here will be used in four places:
- For an application that HYPR auto-creates in the Okta Admin Console
- For the web account name that users will see in the HYPR Mobile App
- For the HYPR Device Manager page where users register their devices
- For internal identification of this integration within the HYPR platform
You can use any name you like, but it's best to go with something that indicates the purpose of the application; for example:HYPRPasswordlessOktaSSO.
Note that any spaces or special characters will be automatically removed from the name you supply. The namespace is limited to 23 characters.Okta Tenant URL The base URL you use to access Okta. For example, if your Okta Admin Console is at https://myorg.okta.com/admin/dashboardthen enter the following:myorg.okta.comOkta API Token An Okta-generated token that grants HYPR the necessary access to your Okta account. See Setting Up Okta. -
Click Add Integration to begin. If the action is successful, you'll see the Integration Added confirmation dialog.
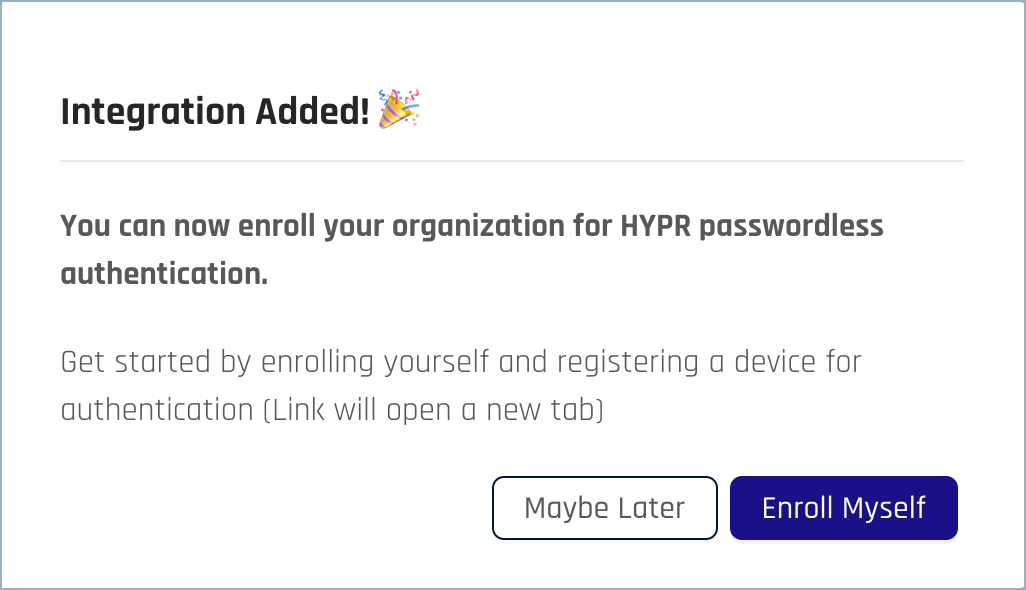
-
You can optionally now register to use OIE yourself by clicking Enroll Myself. You'll be taken to the HYPR Device Manager, where you can register with your chosen device.
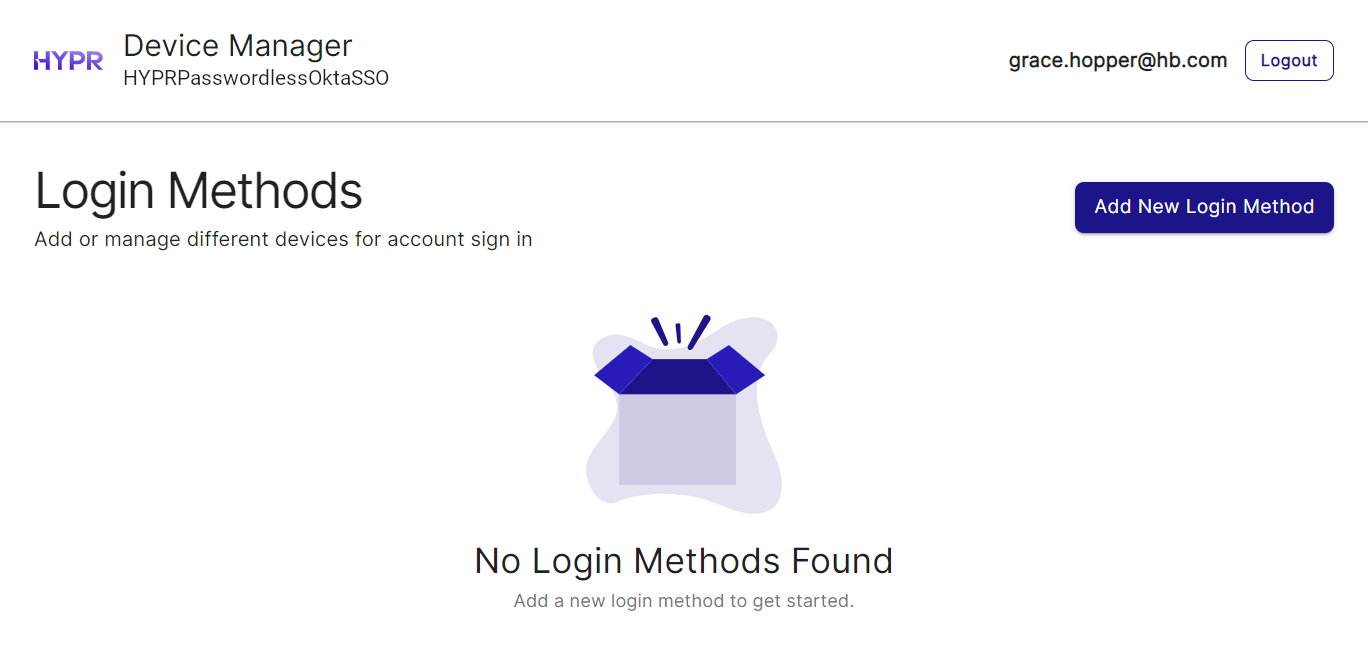
Once you've registered a device, you'll see your username in the list of enrolled users.
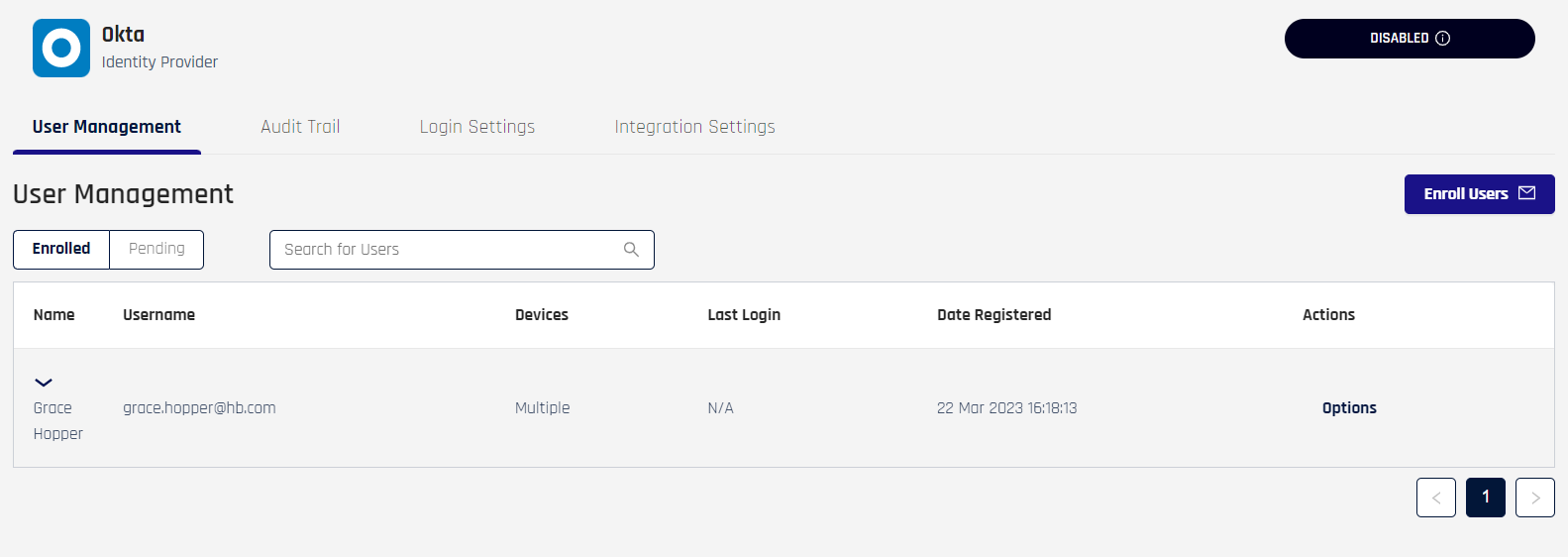
Continue with the HYPR Integrations common UI experience in the Integrations main page to complete Enabling your integration, enrolling users, and monitoring activity with the integration's Audit Trail.